BLUF (Bottom Line Up Front)
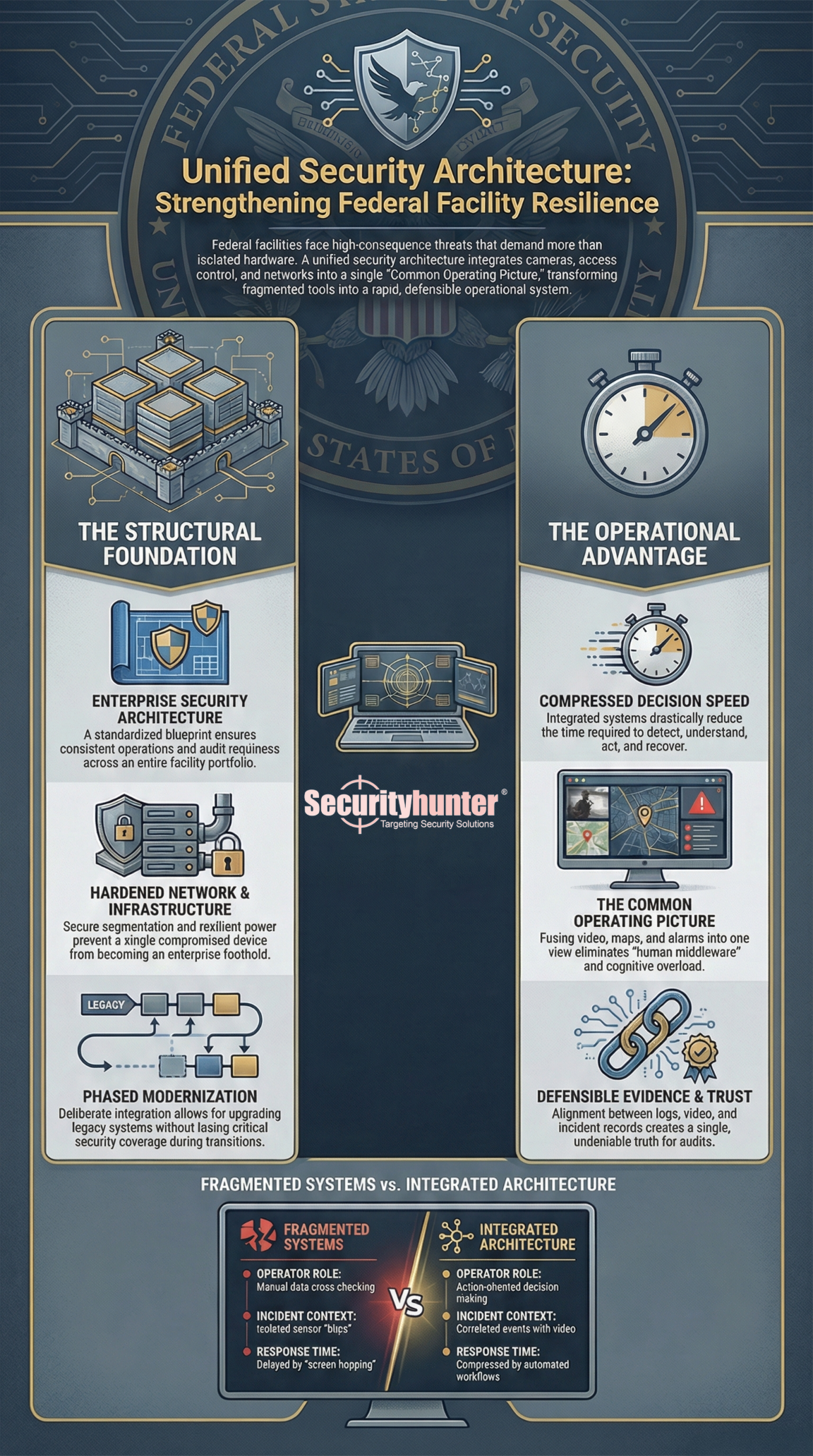
In federal facilities, security systems are only as strong as their integration. Fragmented cameras, access control, alarms, networks, and command center tools create blind spots and slow response. A unified security architecture with strong network, infrastructure, and command-and-control integration delivers faster detection, clearer decisions, defensible evidence, and mission continuity during real-world incidents.
Table Of Contents
Why Federal Facilities Demand Systems Integration
Federal sites operate under higher consequence, higher scrutiny, and longer lifecycles than typical commercial environments.
They face real threats, not hypothetical ones. They also face operational friction that grows over time.
- Multiple tenants and missions in one footprint
- Older systems that cannot be replaced overnight
- Strict compliance, inspection, and audit requirements
- Evidence requirements that must stand up to review
- Continuity expectations during emergencies
In this environment, security is not a set of devices. It is an operational system. Integration is what turns hardware into capability.
Integration Is About Decision Speed
During a security event, the winning factor is time.
- Time to detect
- Time to understand
- Time to act
- Time to recover
Integrated systems compress all four.
Integration Is Also About Trust
Federal security teams must prove what happened.
- Who opened the door
- When it happened
- What the camera saw
- What alarms fired
- What actions operators took
If systems disagree, the story breaks. Integration creates alignment across logs, video, alarms, and incident records.
Security Infrastructure And Systems Integration
Multi System Integration Across Security Platforms
Most federal facilities operate a mix of platforms.
- Access control
- Video management
- Intrusion detection
- Perimeter sensors
- Intercom and duress
- Visitor management and badging workflows
- Mass notification and incident management
Without integration, operators become human middleware. They jump between screens, hunt for cameras, cross check badge data, and call other teams manually. That wastes time and invites error.
With integration, the system automatically provides context.
- Alarm triggers
- Nearest cameras appear instantly
- Door status and last credential used are shown
- Related events are correlated
- Operator workflows prompt next actions
Why Correlation Beats Isolated Alarms
Isolated alarms create noise. Correlated events create insight.
A forced door alarm plus motion detection plus camera analytics is a higher confidence incident than a single sensor blip. That means fewer false dispatches and faster real responses.
Integration Of Legacy And Modern Systems
Federal facilities rarely have the luxury of a clean slate. They modernize in phases.
- A new operations center might be built this year
- Cameras might be replaced over three budget cycles
- Access control panels might be upgraded by building priority
- Perimeter upgrades might lag behind interior modernization
If you do not engineer legacy and modern integration deliberately, you get a patchwork that is fragile and expensive to maintain.
The Goal Is Modernization Without Mission Disruption
The right integration approach supports phased upgrades without losing coverage.
- Keep what still works
- Replace what increases risk
- Build integration layers that reduce vendor lock in
- Sequence cutovers so critical coverage stays online
Enterprise Security Architecture
Enterprise security architecture is the blueprint that ensures every site works the same way and scales across the portfolio.
It defines how systems connect, how data is protected, how access is governed, and how monitoring is sustained.
What Enterprise Architecture Controls
- System boundaries and trust zones
- Identity and role based access
- Approved interfaces and integration standards
- Logging, monitoring, and retention rules
- Resilience and failover expectations
- Configuration control and change governance
Why It Matters For Federal Portfolios
Without architecture, each site becomes its own custom build. That increases risk, cost, and audit pain.
With architecture, you get standardization, predictable operations, and consistent reporting across all facilities.
Command Center And Operations Center Integration
Federal facilities often separate functions that must work together in a crisis.
- Physical security
- IT and cyber operations
- Facilities and building automation
- Mission operations
- Emergency management
During an incident, separation slows response and creates conflicting narratives.
Integration Builds A Common Operating Picture
Operators and leaders need one view of the truth.
- Where the event is
- What systems confirm it
- What actions are underway
- What escalation path is active
- What resources are responding
When command integration works, response becomes coordinated rather than parallel chaos.
Network And Infrastructure Support
Secure Network Design For Security Systems
Every camera, panel, sensor, and workstation is on a network. If the network is weak, the security posture is weak.
Secure design typically includes:
- Network segmentation so security systems are isolated from business IT
- Strong authentication for admins and devices
- Encrypted management channels where possible
- Central monitoring of device health and anomalies
- Controlled remote access with strict governance
- Reliable time synchronization so logs align
Why This Matters For Federal Facilities
It reduces the risk of a compromised device becoming an enterprise foothold. It also improves reliability. Security systems are operational systems, not best effort networks.
Infrastructure Upgrades And Modernization
Many federal security failures are not software failures. They are infrastructure failures.
- Insufficient bandwidth causing video drops
- Aging network closets with overloaded circuits
- Poor grounding leading to intermittent device faults
- Conduit and pathway limits that block expansion
- Building to building links that cannot support modern telemetry
Modern Sensors Demand Modern Infrastructure
Higher resolution video and analytics require more throughput. Situational awareness platforms require reliable data flow. Command decisions require trustworthy telemetry. Infrastructure is what makes those things real.
Power, Cabling, And Communications Support
Power and communications are the physical backbone of security.
- If power is unstable, systems reboot.
- If cabling is poor, video drops and logs desync.
- If communications lack redundancy, central monitoring fails during a crisis.
In federal facilities, resilience is not optional. It is engineered.
Command And Control Environments
Security Operations Centers
A security operations center is where detection becomes action.
A strong SOC is built around workflow, not screens.
What A High Performing SOC Delivers
- Rapid triage with auto pulled context
- Clear escalation and decision prompts
- Consistent incident logging
- Evidence handling that is defensible
- Visibility into system health and blind spots
Central Monitoring Facilities
Central monitoring is how multi site federal portfolios scale without duplicating every function at every building.
Why Central Monitoring Matters
- Consistent response playbooks
- Standardized reporting to leadership
- Shared visibility across regions
- Better staffing efficiency with stronger coverage
Central monitoring only works if connectivity, segmentation, and governance are engineered correctly.
Situational Awareness Platforms
Situational awareness platforms fuse multiple data streams into one operational picture.
- Maps and floorplans
- Camera views and recorded clips
- Access events and credential history
- Intrusion and perimeter sensor alerts
- Incident tickets and response actions
- Facility status data where appropriate
The Benefit Is Faster, Cleaner Decisions
Situational awareness reduces cognitive load. It also improves after action review because events and actions are captured in one place.
What Good Looks Like In Practice
A Single Event With Full Context In Seconds
A forced door alarm occurs at a restricted area entrance.
The system automatically shows:
- Nearest camera views and recent recording
- Door state and last credential used
- Any recent failed access attempts
- Associated motion or perimeter alerts
- Operator workflow with escalation choices
The operator is no longer hunting. They are acting.
Modernization Without Losing Coverage
A facility upgrades cameras and access control in phases.
The integration layer ensures:
- Old and new systems feed the same SOC workflows
- Reporting remains consistent across the cutover
- Operators do not retrain every time a component changes
- Evidence remains aligned across the transition
Common Integration Failures To Avoid
One Off Integrations That Cannot Scale
A custom connector that works at one site becomes technical debt across a portfolio.
Ignoring Network And Power Until The End
If the foundation is weak, the best security platform will still fail under load.
Too Many Screens And No Workflow
Operators overwhelmed by interfaces respond slower, even with good tools.
No Time Synchronization
If clocks drift, logs and video do not align. Evidence becomes questionable.
Vendor Lock In By Design
Closed interfaces limit future flexibility and inflate lifecycle costs.
No Sustainment Model
If patching, configuration control, and monitoring are not planned, the system degrades quietly until an incident exposes it.
Leadership Questions That Expose Weak Plans
What Architecture Governs The Whole Enterprise
Ask to see the enterprise security architecture and how sites align to it.
How Does The Integration Layer Prevent Lock In
Ask which standards, interfaces, and data ownership models are used.
What Is The Network Segmentation Strategy
Ask where security systems sit in the network and how access is controlled.
What Happens During Power Or Network Loss
Ask for the failover story, redundancy design, and testing evidence.
How Is Performance Validated Before Cutover
Ask how end to end testing is conducted without disrupting operations.
What Metrics Will You Report Monthly
Ask for measurable outcomes like uptime, alarm response times, and device health.
Summary
In federal facilities, systems integration is not a nice-to-have. It is the core of security performance. Multi-platform integration reduces blind spots and speeds response. Legacy modern integration enables phased modernization without mission disruption. Enterprise architecture creates consistency and audit readiness across the portfolio. Network, infrastructure, power, and communications engineering ensure system reliability. Command-and-control integration turns tools into coordinated action.
If your facility security stack still runs as separate systems, you are operating with built-in delay and built-in blind spots. The fix is not buying more devices. The fix is to design the architecture, integrate the platforms, harden the network foundation, and build command center workflows that deliver context in seconds.